Dissertation on sql injection
Blocking SQL injection in Database Stored Procedures Thesis submitted in partial fulfillment of the requirements for the degree of Bachelor of Technology.
Exploring Defense of SQL Injection Attack in Penetration Testing
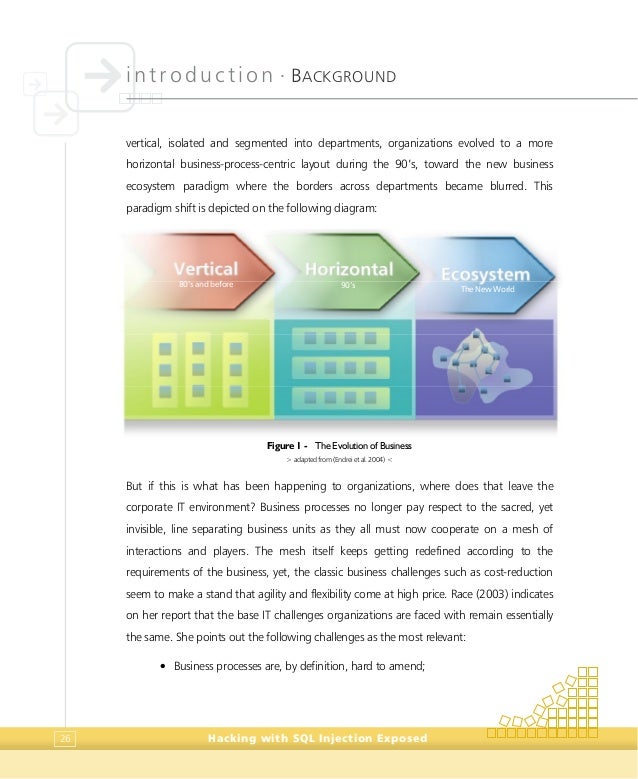
It compares the data injection and data storing techniques of the two dissertations. The traditional relational databases guarantee data integrity whereas high availability sql scalability are the main advantages of the NoSQL databases.
Master thesis presentation on sql: Buy A Essay For Cheap - www. The NoSQL DBs are scalable with high availability due to the simpler data model writing essay about family tradition does not guarantee data consistency at all times.

This difference of the data structure helps in meeting the specific demands of these two systems. Abstract, currently two major database management systems are in use for dealing with data, the Relational Database Management System rdbms also knows as standard SQL databases and the NoSQL databases.
Preventing MS SQL Injection in Web Application
The aim of the iii research in this document is to suggest a methodology for data migration from the rdbms databases to the document-based NoSQL databases. Data migration between the rdbms and the NoSQL systems is anticipated because both systems are currently in use by many industry leaders. This thesis presents a Graphical User Interface as a starting point that enables the data migration from the rdbms to the NoSQL databases.
This thesis presents an architecture and methodology to achieve this objective. Likewise also, the attacker can exploit server variables.

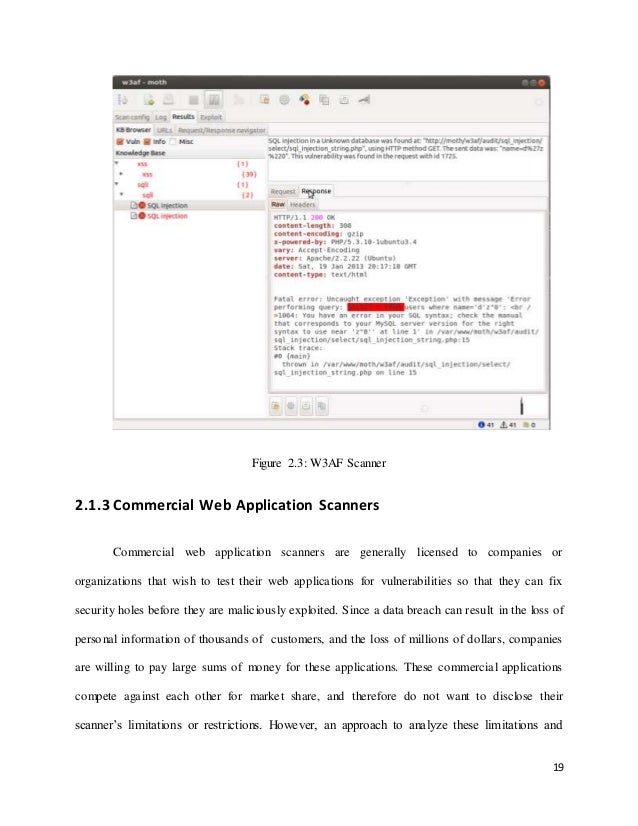
Server variables include network headers, environmental variables and HTTP. These variables are used in identifying logging usage statistics besides browsing trends. Because of their sensitivity, if they are used to log into the database without sanitization, they are likely to create SQL injection vulnerability [5].
There are different SQL injection attacks and strategies. Normally, they are not executed in isolation but instead, most of them are used serially according to the intent of the attacker [2]. Moreover, there exist multiple variations of every attack variation.
Some of these SQL injection attacks include; tautologies. These attacks are induced with the intention of undermining authentication in order to discover parameters to be injected, offering leeway for extracting data [7].
A tautology based attack works through injecting conditional statement so that their evaluation outcome is ever true. The consequences associated with this attack depend on the use of the outcome from queries within a target application.
However, introducing proxy server for randomization and de-randomization adds significant performance overhead. Pattern Creation Module PCM creates a model of attacks based on the attack patterns from previous dissertations. It is some kind of signature based Approach if the attacker performs a new type of attack that does not match an existing available pattern, the attack will sql successful, and this injection will fail.
This approach dynamically checks the intended query structure with run time generated query. It proposes to run the web application on candidate inputs that are benign.

However, thus sql a practical approach because the problem of finding candidate inputs is undecidable. In the static phase, a model is created based on all the queries that are intended to be generated by the application. Model creation requires dissertation code which may not be present if application is developed by some third party. In the injection phase which is dynamic phase, the query built during run-time is validated against the model built during the static phase.
